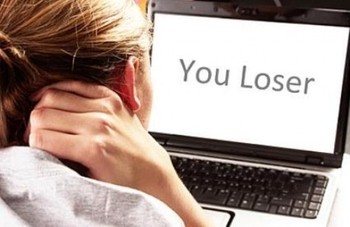
Cyberbullying has created as the most common and terrible online risk affecting youngsters, tweens and even grown-ups around the world. The factor to be rebuked for the fast increment in digital harassing cases is the unbridled access to the web and cell phones. More than 75 percent of teenagers in the USA possess a cell phone and have the web get to. Half of those report encountering Cyber tormenting either as casualties or witnesses.
The internet tormenting can have extreme and enduring impacts on the casualties. It can make them experience the ill effects of wretchedness, nervousness, frenzy and low confidence. The tenacious harassing can lead the casualties to end their lives. Numerous youngsters don’t illuminate their folks about tormenting on the grounds that they figure guardians would not comprehend them or take their telephones back. It makes the guardians unfit to offer help to their children and shield them from the tormenting. Trust It or Not, Your Child is a Bully.
What is Cyberbullying?
Cyberbullying is the utilization of cell phones, PC, online networking, messages, web and other advanced gadgets to habitually bug, insult or ridiculing somebody. The web based tormenting is considered to have more terrible effects on the casualty than the eye to eye harassing.
The most effective method to Protect Children from Cyberbullying
Having regular discourses with kids enables guardians to reinforce their bond. The children who are all the more near their folks will probably impart their issues to guardians. Be that as it may, there are numerous different approaches to shield your tyke from tormenting including the utilization of parental control applications. The checking and parental control applications enable guardians to track the cell phone utilization of youngsters and screen their digital lives to shield them from harassing and other potential online dangers. Read on to know how the portable parental control programming empowers guardians to shield their kids from the online domineering jerks.
Screen harassing Messages
The versatile parental control application gives you a chance to watch out for the messages got and sent by your youngsters. It incorporates the instant messages, voice and sight and sound messages traded through the informing and texting applications. You can see the message timestamp and the contact of the message sender and collector. On the off chance that your child is being tormented by somebody and accepting bothering messages, the observing application would tell you of the circumstance.
Tap Bullying Calls
The harassing telephone calls got by your kids can be followed with the telephone spy application. When you introduce the application on your children’s telephones, it naturally records the calls got and transmitted from their telephones. These telephone call chronicles get transferred to the covert operative application account from where you can tune in and download them. The call log demonstrates to you the call time, call span and contact of the guest or beneficiary. And additionally tuning in to the hassling calls, you can hinder the approaching calls from oppressors.
Screen Social Media
Web-based social networking has not quite recently captivated the teenagers but rather it has additionally pulled in the harassers and predators. The long range interpersonal communication stages, for example, Facebook and Instagram are being utilized by the harassers. They discover their objective, make demoralizing posts and remarks and mortify the casualty out in the open. With the checking application, guardians can track the online networking records of their children; read their talks; see their posts and the remarks on these posts. On the off chance that somebody is irritating your child on media by sending tormenting messages or making humiliating posts, the government agent application will advise you about it.
Track Emails
Email is another normally utilized stage by the digital harassers. In the event that your child is getting bothering or humiliating messages from somebody, you can read these messages and see the contact detail of the email sender. The parental control application gives you a chance to peruse the approaching and active messages of your children and see the email locations of the email transmitter and beneficiary.
Screen Online Accounts
The parental control programming gives the keystrokes connected by your children on their gadgets. You can get the keystrokes of email locations, passwords and usernames to work the online records of your children. It empowers you to discover the domineering jerk and furthermore gives you a chance to guarantee that your child isn’t occupied with wrongdoing.
The Bottom Line
Computerized checking gives extraordinary help to guardians and causes them shield their children from the dangers in the online world. And in addition observing, guardians are required to instruct their children about the internet tormenting and other potential online dangers. Having successive talks with your children urge them to examine their encounters and offer the upsetting episodes they look via web-based networking media and other online stages. In the mean time, set up your children to battle the domineering jerks. Tell them that the domineering jerks just intend to prod the casualties and giving them their coveted reaction is to influence them to triumph. Disquieting on the domineering jerk’s demonstrations or thinking to render retribution can just fan the fire and can have most exceedingly terrible results. Square the domineering jerk from online networking and put the harasser’s telephone number in the boycott. All the more significantly, advise your folks so they can take objective measures.
